when India had always planned to announce its ban on TikTok, along with 58 other Chinese apps, on June 29, or was prompted by the viral response to the iOS security issue is not known. But, as things stand, TikTok has been pulled from the App Store and Play Store in India, its largest market, and has seen similar protests from users in other major markets around the world, including the U.S.
One of the more unusual groups campaigning against TikTok is the newly awakened Anonymous hactivist group. As ever with Anonymous, it’s difficult to attribute anything to the non-existent central core of this loosely affiliated hacker collective, but one of the better followed Twitter accounts ostensibly linked to the group has been mounting a fierce campaign against TikTok for several weeks, one that has now gained prominence given the events of the last few days.
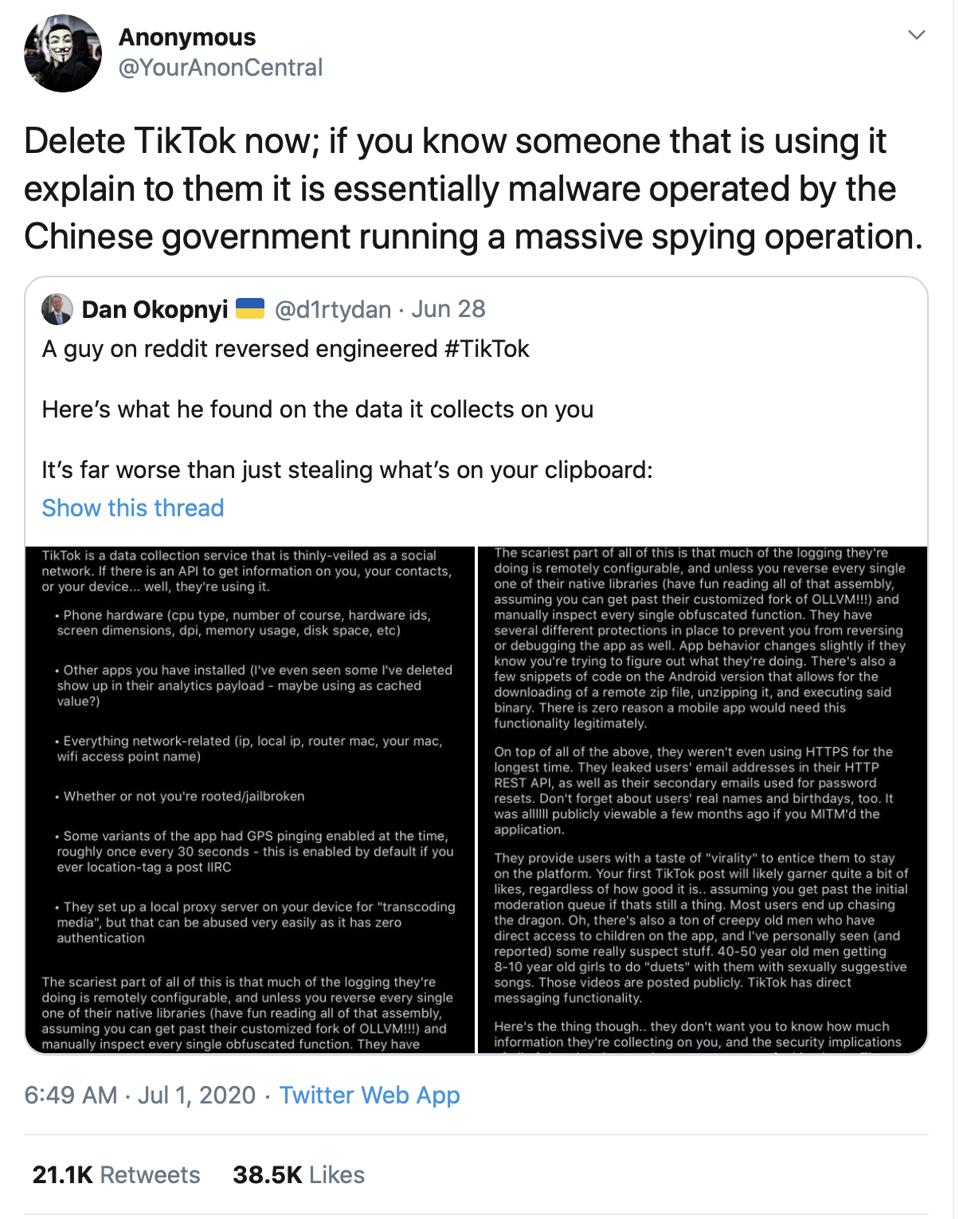
The original issue that prompted Anonymous to target TikTok appears to be the “misrepresentation” of Anonymous on TikTok itself, with the setting up of an account. “Anonymous has no TikTok account,” the same Twitter account tweeted on June 6, “that is an App created as spyware by the Chinese government.”
Those affiliated with Anonymous take exception to copycat accounts, which is complicated by the lack of any central function. In the aftermath of the Minneapolis Police story, someone affiliated with the group took exception to a Twitter account that was monetising the brand, telling me: “We do not appreciate false flag impersonations. There will be consequences.”
This has now become an interesting collision of two completely different viral stories in their own right. Anonymous hit the headlines a month ago, when the “group” seemed to mount a comeback in the wake of the killing of George Floyd. A video posted on Facebook threatened to “expose the many crimes” of the Minneapolis Police unless the officers responsible were held to account.
There have been various stories since then, with reports of DDoS attacks on police service websites, the hacking of data and even the compromise of radio systems. But, as ever, with Anonymous, it is always critical to remember that you are seeing that loose affiliation of like-minded individuals, with Anonymous used as a rallying cry and an umbrella for claims and counter-claims. Attribution, as such, is not possible.
This also puts TikTok in the somewhat unique position of having united various governments, including the U.S., and Anonymous behind the same cause.
For TikTok, whether there is any hacking risk following these social media posts we will have to wait and see. Again, you have to remember the way this works. A rallying call has gone out to like-minded hacking communities worldwide. A target has been named and shamed. It would not be a surprise if claims of hacks or DDoS website attacks followed. That’s the patten now.
So, why does this matter? Well, it’s one thing for the U.S. government or even the Indian government to warn hundreds of millions of users about the dangers of TikTok, but various celebrities and influencers have also been swayed by the latest claims and have publicly expressed their concerns. Anonymous is a viral movement that is targeting some of the same user base that has driven TikTok’s growth. It is campaigning against TikTok, and that campaign will drive its own viral message.
And while until now that user base has remained steadfastly resilient to any of those warnings, sticking with the video sharing app in droves, you can start to get the feeling now that come of this might stick. It’s subtle, and it’s always risky to judge the world by the twitter-sphere, but there’s a change now in the wind.
Reference : www.forbes.com
Comments
Post a Comment